I had that recently using Apex. Every time I ran to lunch, did other things, watched the grass grow... I came back to find my Application Builder had timed out.
It's frustrating to have to log in again, and doubly frustrating to find you're back at Apex Home, not where ever you were.
It took all of 30 seconds to find the correct setting, but I thought I'd share anyway for those who may be newer to the tool.
First log in to your INTERNAL workspace, or visit
http://localhost:7777/pls/apex/apex_admin
in lieu of your usual
http://localhost:7777/pls/apex/f?p=...
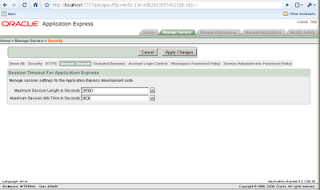
Under Home -> Manage Service -> Security, there is a section on Session Timeout.
I've modified my maximum session idle time to be the same as my maximum session length. When working from home, this is more than suitable. In a work environment (hmm, my home should be included in this category), you ought to negotiate with the powers that be.
There are similar settings at Application level through Shared Components -> Security. And as with most settings, it may be modified programatically at runtime using Apex_Util.
If you are having a non-mathematical day, you can use the following SQL query to work out how many seconds you want - 86400 is the number of seconds in a day. This query represents midnight plus however many seconds.
SAGE@sw10g> select trunc(sysdate) + 3600/86400 from dual;
TRUNC(SYSDATE)+3600
-------------------
27-01-2010 01:00:00
1 row selected.